The tables have turned. Unlike in traditional times where the authorities were well ready to catch a bandit galloping away on a dusty trail with a sack of loot, modern criminals today use constantly changing code as weapons and proxies as masks to stay ahead of the authorities.
Cyber criminals of today, leave yesterdays bank robbers in the dust.
Reinforced cement walls and titanium vaults of the past have now become mere pieces of software designed to keep intruders out.
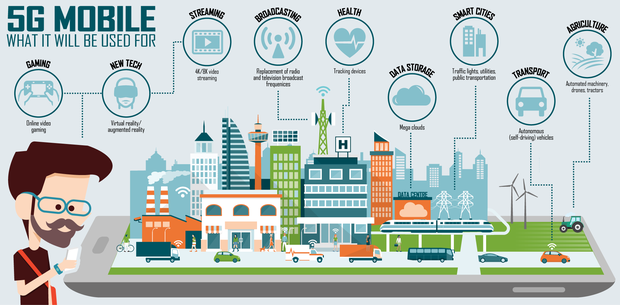
While steering humanity towards a more efficient and secure way of banking, the rulers of today work endlessly in trying to solve the security puzzle. The ultimate goal for the ruling elite is to move to a cashless society. A society where wallets have become vaults. Where bank tellers became secure websites. Where passwords become biometrics. And ultimately, where RFID implants come to destroy the ways of the forgotten wild west.
Until then, however, criminals today still have the uncanny ability to quickly adapt to an ever-changing environment and, therefore, so should we. Thoughts of protecting our hard earned money lingers in the back of our minds on a daily basis. Statistics show that bank fraud soared to over 1 trillion dollars yearly in the new millennium, and this figure still grows today. We all have some common knowledge on how to keep crooks out of our virtual pockets, but is it enough?
It could happen to you. Counter measures introduced by banking institutions vary depending largely on the circumstances around the occurrence. Even with the best online banking security tips in mind, the fraudster is always lurking for new opportunities. Should you fall victim to bank fraud, your institution may need to take it to the extreme, in order to keep your (aka their) money safe. For example, if your personal computer was the compromised source of the fraudulent transaction, your bank may deactivate your account until it is verified that your computer has been professionally cleaned. Now, that's frustrating. Money stolen, and now, locked away. Some companies, like Tech!Espresso Computer Repair in Calgary, for example, have started an initiative for offering a service specially designed to help you out. They wrap a trusted verification certificate around their in-home computer virus removal service to help the bank identify that your computer has been inspected and cleaned by a certified expert. The customer simply needs to book the service and show the certificate to the bank representative upon completion, to have the account reactivated. That may be great news in regaining access to your funds, but the problem at hand has still not been resolved.
The following tips are things you can do every day to ensure the protection of your personal information.
The number one rule is follow your gut feelings; if you feel like a situation is suspicious, then you are more than likely to be correct.
• Verify the identity of anyone asking for personal or financial information; do not give it out automatically to anyone who asks for it.
• If your debit/credit card or check book is lost or stolen, notify Farmers Savings Bank & Trust immediately.
• Be sure to review monthly statements for suspicious activity. Report anything you find to Farmers Savings Bank & Trust.
• Shred any financial documents or documents with personal information on them before recycling them.
• Memorize your Social Insurance Number; do not carry your card around with you.
• When online shopping check the address bar to ensure the website starts with ”https” AND has a padlock there or at the bottom of the browser window before entering any payment information.
• If you have not gotten your regular bills from a company, notify them that you have not received them.
• Check your credit report annually.
What to do if your identity has been stolen and you have fallen victim to bank fraud
• Place a fraud alert on your credit reports by calling the three major credit reporting agencies (Equifax, Experian and Transunion).
1. Contact your Bank so they can help you block the affected accounts.
2. Contact the Government office that issues your ID.
3. Call your local police department and file a police report. If the fraud occurred in a different area, you can try filing a report with the local police department there as well.
How to Spot a Phishing Scam
• Phishing scams have become a favourite tool of online criminals to steal your usernames, passwords, credit card information and even money. In a phishing scam, you will receive an email that looks like it is from an authoritative source. While it may seem genuine, a phishing email contains several clues that it should not be trusted:
• The "From" field: You most likely will not recognize the email address. It may also be an odd spellings of an authoritative email, such as the following examples "support@micrsoft.com" or "IT@abay.com".
• The "To" field: Phishing scams are generally sent to either random email lists or a bunch of people at the same company with names that start with the same letter.
• Email subject line: Watch out for vague subject lines, subject lines advertising a deal that is too good to be true or has a limited time span, or emails that "require your immediate attention".
• Email body: Lots of grammatical errors signifies a phishing scam. You can also check if the body of an email is an image by clicking and dragging. If it is an image, the email is definitely a scam.
• Links: To check the legitimacy of links in an email, hover over them to see their destination address. If it is something random or an address you do not recognize, DO NOT click on it.
• Attachments: DO NOT open attachments in an email unless it is from a trusted source. These attachments can have viruses or trojans that can access your personal information. Risky attachments have file extensions like .exe, .scr, .zip, .com, and .bat.
• A request for personal information: Financial institutions will generally never send an email asking for personal or account information. Emails are not secure, meaning your personal information can be intercepted. Any email requesting you send personal information via email should be deleted immediately.
Have you fallen victim?
It's hard stay safe and remember to cover all bases regarding the safe-keep of your finances and the information guarding them all of the time! If you have fallen victim, or would like some help guarding your computer — let us help!
Secure My Computer